Most "hardware wallet" marketing claims keys never leave the secure element. That's true on chips like the SE050 that do native Schnorr — but the ATECC608B we ship today doesn't sign Schnorr. So we'll tell you exactly what happens.
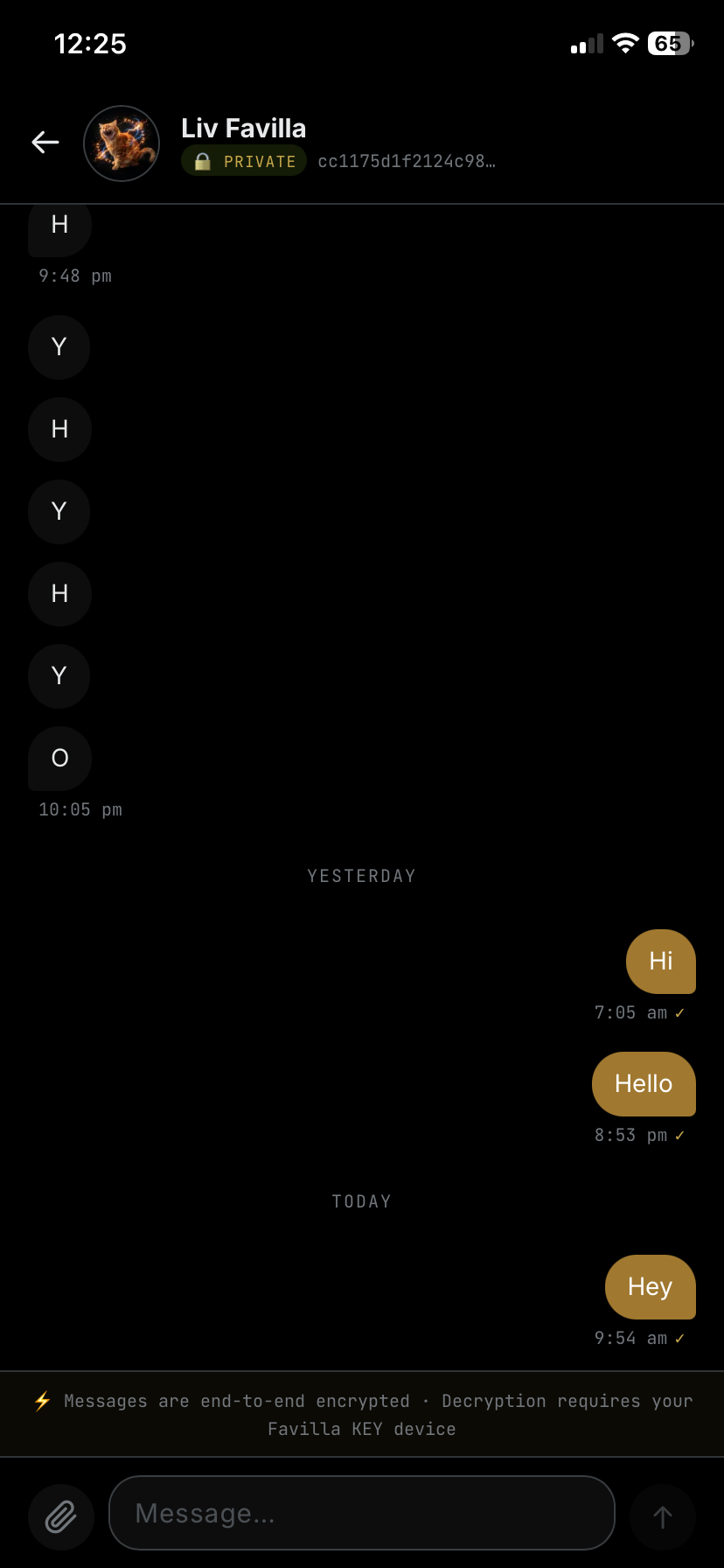
Your nsec is generated on the device and stored encrypted on a Microchip ATECC608B, behind a PIN with brute-force lockout. When you approve a signature, the ATECC unwraps the key into the ESP32's RAM. The ESP32 performs the Schnorr signing operation. Then it zeroes the memory.
The key is never written to flash. It never touches a network. It never enters a browser. It exists in volatile memory for milliseconds at a time, on a device that does nothing else.
Is this as strong as a chip that signs natively? No. Is it dramatically stronger than your nsec sitting in localStorage on every site you've ever pasted it into? Yes — by an enormous margin. The SE050 with native Schnorr is on the v2 roadmap.
We'd rather ship something honest than something that overstates its threat model. The architecture is no different from Krux or SeedSigner — well-understood, open-source, ESP32-based signing.
Engineering Note 04